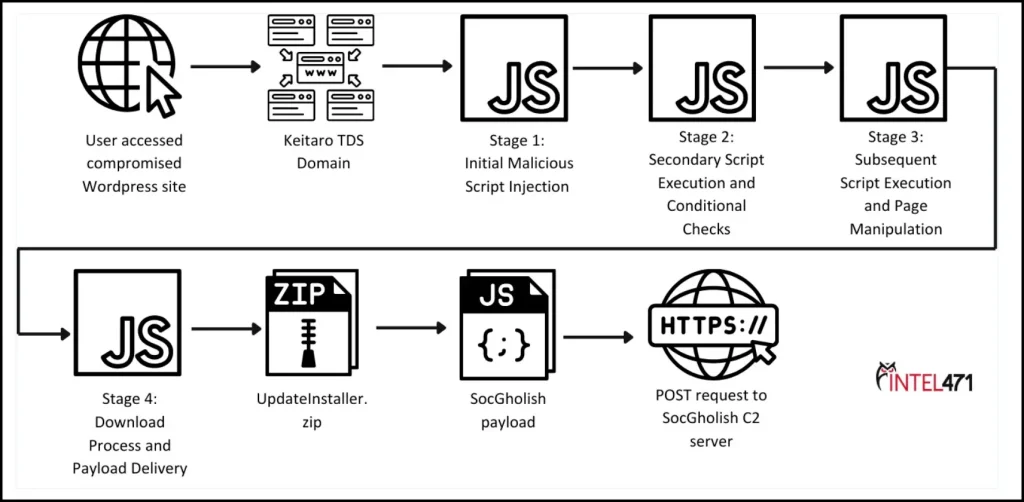
An illustration of the steps that lead to a SocGholish infection. | Source: Intel 471
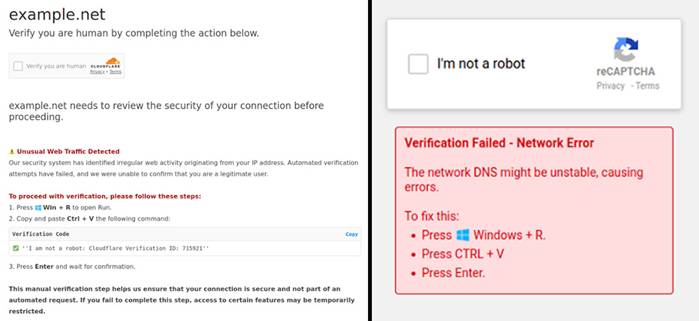
Threat actors have once again intensified the distribution of the SocGholish malware, disguising it as browser updates. According to intelligence from Intel 471, attackers leverage compromised websites to lure users into downloading ZIP files containing malicious scripts. This tactic enables cybercriminals to circumvent conventional cybersecurity measures and disseminate malware among unsuspecting victims.
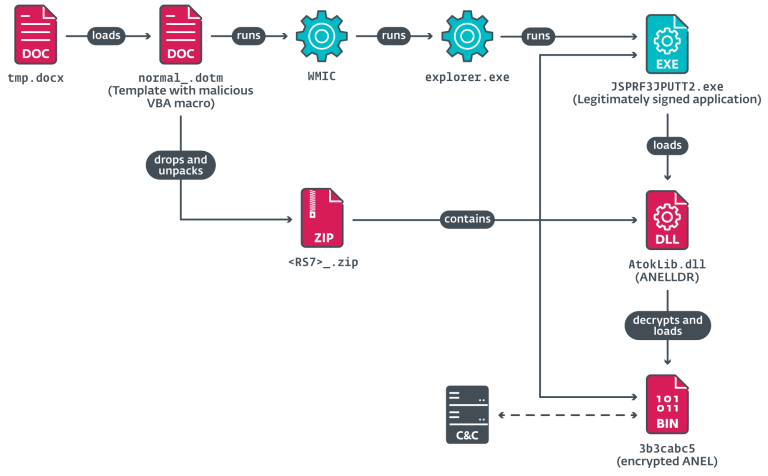
SocGholish serves as an initial access tool for cybercriminals, embedding malicious scripts into legitimate websites that subsequently appear in search engine results. When a user visits such a site, they are presented with a fraudulent browser update notification. Upon downloading and extracting the ZIP file, the embedded malicious code is executed, triggering a broader infection chain.
Analysis reveals that SocGholish tailors its attack strategy based on the victim’s device. Embedded scripts assess the operating system and browser type before determining whether to display the fake update prompt. This adaptive approach significantly enhances the effectiveness of the attack, allowing adversaries to evade detection on non-targeted devices.
The attackers’ primary objective remains the deployment of additional malicious components onto the compromised system. The ZIP archives, masquerading as software updates, frequently contain obfuscated JavaScript files designed to download and install remote access trojans (RATs), administrative backdoors, and even ransomware. Among the commonly deployed tools is Cobalt Strike, which enables cybercriminals to navigate within a network and escalate privileges.
A pivotal element in the proliferation of SocGholish is the use of Domain Shadowing. Attackers infiltrate legitimate domains and create malicious subdomains, which are subsequently employed to distribute infected files. Additionally, intermediary servers facilitate the covert transmission of payloads, further complicating detection efforts.
Research suggests potential ties between SocGholish campaigns and Evil Corp, a notorious cybercrime syndicate known for deploying banking trojans and ransomware. This group reportedly utilizes SocGholish as a foothold to infiltrate systems, subsequently monetizing the attack through financial extortion.
According to analysts, in just one week at the end of 2024, over 1.5 million user interactions with SocGholish-linked malicious resources were recorded—underscoring the scale of the threat and the alarming efficiency of these campaigns.
To mitigate such attacks, cybersecurity experts advocate for rigorous precautionary measures. It is crucial to verify the authenticity of software updates, deploy advanced threat detection solutions, and routinely audit web resources for potential compromises. Organizations should implement traffic monitoring and anomaly detection systems to swiftly identify and neutralize suspicious activities.