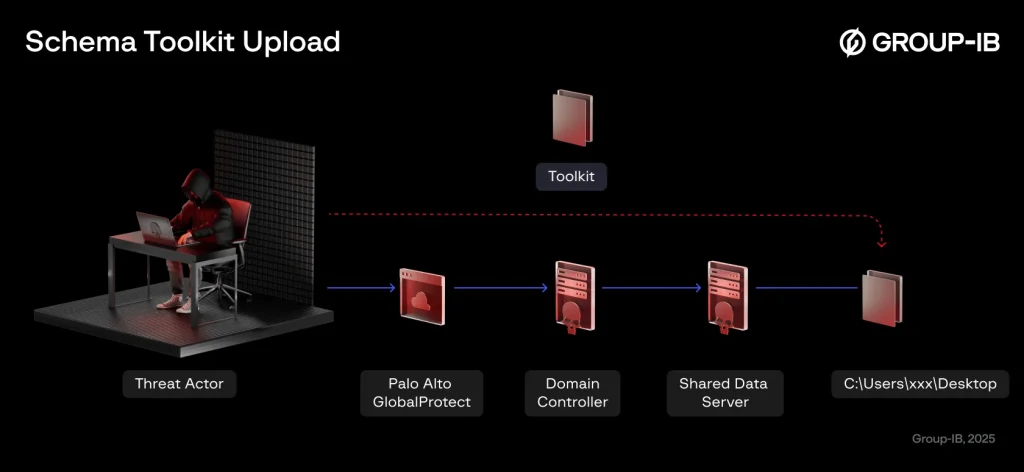
Toolkit upload schema | Source: Group-IB
In 2024, a formidable new player emerged on the cybercriminal landscape—RansomHub, a ransomware group that has already targeted more than 600 organizations worldwide. According to research by Group-IB, RansomHub swiftly filled the void left by recent disruptions to ALPHV and LockBit operations.
Experts note that RansomHub operates under the ransomware-as-a-service (RaaS) model, aggressively recruiting affiliates on underground forums such as RAMP. A key strategy has been luring hackers previously affiliated with rival groups, enabling RansomHub to rapidly scale its attacks.
Analysis of the malware’s code suggests that the group likely acquired its ransomware from Knight (Cyclops), another notorious cybercriminal organization. The adoption of pre-existing tooling accelerated the deployment of attacks, while the malware’s cross-platform capabilities allow it to encrypt systems running Windows, ESXi, Linux, and FreeBSD—broadening the range of potential victims.
RansomHub exhibits a high degree of operational sophistication. The group employs both conventional attack vectors—such as exploiting vulnerabilities in VPN services and brute-forcing credentials—and advanced techniques, including zero-day exploits. Among its arsenal are tools like PCHunter, designed to bypass security mechanisms.
The attack methodology involves meticulous reconnaissance of the victim’s network and the exfiltration of its most valuable data. Operators infiltrate infrastructure, seize control over critical nodes—file storage systems, backups, and servers—and transfer sensitive information to external servers. For data exfiltration, attackers rely on FileZilla before initiating encryption across compromised hosts.
Once the attack is complete, RansomHub extorts its victims, demanding payment in exchange for decryption and the non-disclosure of stolen data. The ransomware is capable of shutting down virtual machines, erasing shadow copies, and wiping event logs—significantly hampering forensic investigations.
One of RansomHub’s most devastating operations unfolded in just 14 hours. Exploiting a vulnerability in Palo Alto’s firewall (CVE-2024-3400) for initial access, the attackers then brute-forced VPN client credentials. Subsequently, they leveraged legacy Windows vulnerabilities (CVE-2021-42278 and CVE-2020-1472) to establish full control over the network.
Security experts stress that RansomHub’s effectiveness is largely enabled by organizations’ failure to promptly patch their systems. When a company falls victim to an exploit that was addressed years ago, the blame rests solely on its own negligence rather than on software vendors.
The escalating activity of RansomHub underscores the continuous evolution of cyber threats. Organizations must fortify their defenses, routinely update their software, and minimize their attack surface to avoid becoming the next victim of RansomHub or other ransomware syndicates.