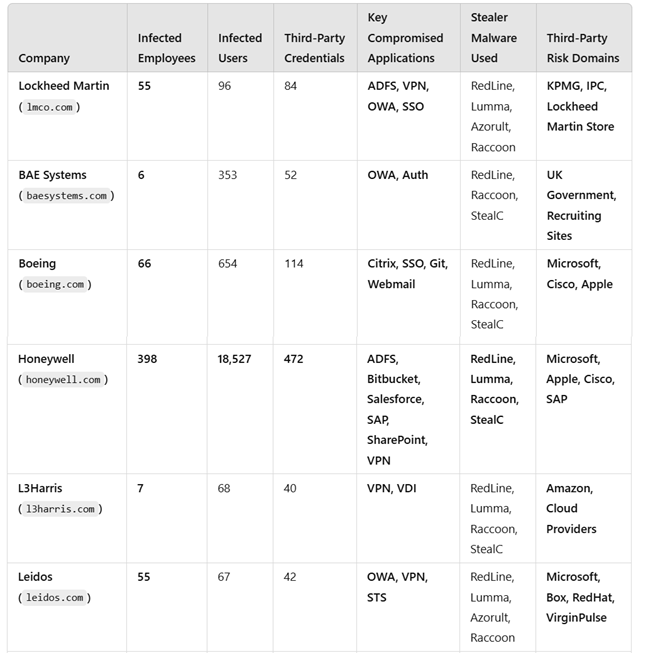
List of Compromised Companies
Billions of dollars, cutting-edge technologies, and the strictest security protocols—none of it was enough to shield American military institutions and defense corporations from a seemingly rudimentary cybercrime.
A Hudson Rock investigation has revealed that dozens of employees from leading military contractors, including Lockheed Martin, Boeing, and Honeywell, as well as personnel from the U.S. Army and Navy, have fallen victim to infostealer malware. As a result, login credentials, VPN sessions, email accounts, and even access to classified procurement systems have landed in the hands of cybercriminals.
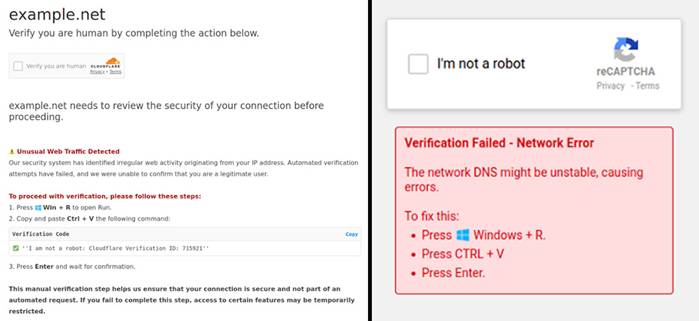
It takes just a single accidental download of an infected file—a game modification, cracked software, or a trojanized PDF document—for the infostealer to infiltrate a system. Once installed, the malware harvests everything: passwords, browser history, and files from the victim’s workstation. These stolen datasets are then sold on the dark web, with full access to a defense contractor’s work computer, complete with confidential data, fetching as little as $10.
This attack vector has proven highly effective. According to Hudson Rock, over 30 million computers have been compromised in recent years, with nearly 20% containing corporate credentials—many from companies directly involved in U.S. national security operations.
A particularly alarming aspect of this breach is the theft of active session cookies, which allow attackers to instantly log into secured systems without needing usernames or passwords. Even multi-factor authentication (MFA) offers no protection if an adversary gains access to an already-authenticated session.
The scale of the crisis is starkly illustrated by Honeywell’s breach. Since 2024, 56 corporate accounts belonging to 398 employees have been compromised, granting unauthorized access to internal SAP, Bitbucket, and SharePoint systems. Additionally, credentials for third-party services, including Microsoft, Cisco, and SAP, have also been leaked. The ramifications extend beyond Honeywell itself, as its partners—Anduril, SpaceX, and Palantir—could also be infiltrated through supply chain vulnerabilities.
Yet, the true threat extends far beyond private enterprises. Among the affected entities are U.S. Navy personnel, whose access to Citrix, OWA, Confluence, and military training platforms has been compromised. This breach opens the door to cyberattacks on critical military infrastructure. Experts warn that if such data were to fall into the hands of adversarial nations, it could facilitate deep infiltration into military operations.
Key Defense Measures Include:
- Prohibiting the use of personal devices for work—many infections originate from systems used for both professional and personal tasks.
- Enforcing strict software download policies—allowing only licensed and verified applications.
- Implementing multi-layered authentication with continuous session monitoring—if session cookies are stolen, they must be immediately invalidated.
- Constantly tracking data leaks on the dark web—organizations must proactively monitor compromised employee credentials.
Hudson Rock acknowledges that infostealers are no longer just tools of cybercriminals; they have become a direct threat to national security. Even organizations adhering to the strictest cybersecurity standards are vulnerable due to weaknesses in their contractors and partners. The question is no longer whether data breaches can be prevented, but rather how quickly they can be detected and neutralized.