Dragos has released its latest cyber threat report focusing on Operational Technology (OT) and Industrial Control Systems (ICS). Now in its eighth annual edition, the report examines the evolving threat landscape, analyzes cybercriminal tactics, and assesses the resilience of critical infrastructure.
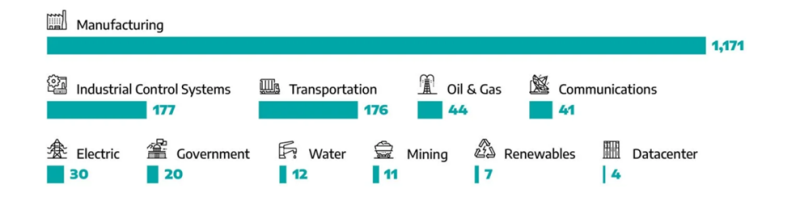
According to the findings, cyberattacks on industrial enterprises have surged at an alarming rate. In 2024, researchers tracked the activities of 23 threat groups targeting OT environments, with nine exhibiting particularly high levels of activity. Two newly identified groups—BAUXITE and GRAPHITE—have been observed targeting the oil and gas sector, water utilities, and logistics networks. BAUXITE employs Stage 2 ICS Cyber Kill Chain methodologies, while GRAPHITE leverages phishing campaigns and exploits vulnerabilities to infiltrate industrial networks.
Additionally, researchers reported an escalation in attacks orchestrated by VOLTZITE, KAMACITE, and ELECTRUM:
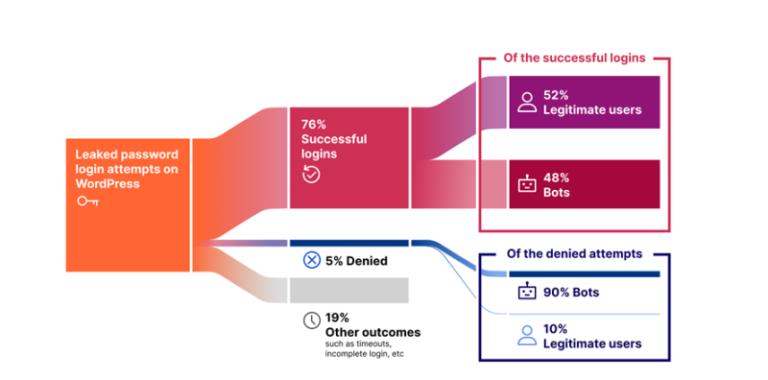
- VOLTZITE focuses on energy and telecommunications infrastructure, utilizing stolen credentials to facilitate future intrusions.
- KAMACITE operates as an Initial Access Broker (IAB), assisting other threat actors in breaching networks.
- ELECTRUM specializes in destructive malware targeting industrial systems, and its latest tool, AcidPour, is designed to physically incapacitate embedded OT devices.
The report also highlights the emergence of two novel OT-specific malware families:
- Fuxnet, which in one incident disabled thousands of monitoring system sensors by exploiting inadequate security measures.
- FrostyGoop, which targeted Ukraine’s energy infrastructure, causing heating disruptions in over 600 residential buildings. This malware interfaced with industrial control devices via the Modbus TCP protocol, making detection exceptionally challenging.
The threat of ransomware-driven extortion has also intensified, with attacks surging by 87% over the past year. In 75% of cases, industrial operations suffered partial disruptions, while in 25% of incidents, production was brought to a complete halt.
Dragos underscores persistent vulnerabilities in OT security. Many organizations lack incident response plans, suffer from ineffective network segmentation, and fail to adequately monitor their OT environments. Even when critical vulnerabilities are identified, they are frequently left unpatched. Furthermore, remote access remains a significant weak point, with over 65% of evaluated facilities permitting unsafe external connections.
To address these challenges, security experts advocate for the “Now, Next, Never” approach to vulnerability management:
- 6% of vulnerabilities demand immediate remediation.
- 63% should be addressed in the near future.
- 31% can be deprioritized without immediate action.
This methodology helps organizations focus on genuine threats rather than implementing patches purely for compliance purposes.
Dragos concludes that cyber threats in industrial environments continue to escalate, with adversaries constantly adapting to defensive measures. Effective protection requires not only advanced technology but also robust risk management, comprehensive personnel training, and a well-defined incident response strategy.