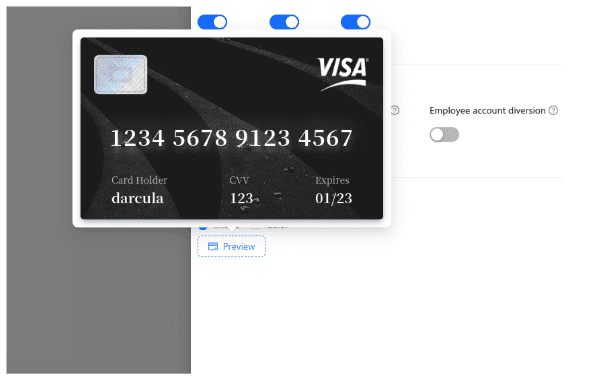
Example of a virtually-generated card from stolen card details
The malicious platform Darcula, which operates under the Phishing-as-a-Service (PhaaS) model, is preparing to launch its third iteration, significantly enhancing its capabilities. Understanding the features of this new version is crucial for assessing contemporary cyber threats and developing effective countermeasures.
A key innovation in Darcula 3.0 is the introduction of a DIY phishing kit generator, enabling users to execute sophisticated attacks that mimic virtually any brand. In the beta version currently undergoing testing, previous limitations have been removed—rather than relying on a predefined set of templates, users can now generate customized phishing kits simply by providing the URL of a targeted website.
At the core of this cloning mechanism is Puppeteer, a powerful automation tool that replicates the structure of an original site, including its HTML, CSS, images, and JavaScript. This allows for the creation of highly accurate replicas with seamless modifications to key elements such as login forms, payment credential input pages, and two-factor authentication interfaces.
Additionally, the Darcula Suite has been upgraded with an enhanced administrative interface, featuring advanced bot-blocking mechanisms, IP filtering, attack performance monitoring, and an intuitive campaign management system. Other notable improvements include an automated system for embedding stolen payment card data into digital wallets and a tool for generating virtual payment cards, facilitating the seamless exploitation of compromised financial information.
Researchers at Netcraft have conducted an in-depth analysis of the Darcula 3.0 beta version and confirmed its advertised functionality. Their findings indicate that between February 5 and February 10, the number of downloads for the containerized images required to operate Darcula more than doubled, underscoring the heightened interest among cybercriminals in this new toolkit.
Darcula first emerged last year, leveraging more than 20,000 domains to target iOS and Android users across 100 countries. With the impending release of Darcula 3.0, Netcraft warns that the scale of phishing attacks could increase dramatically. Over the past ten months, the firm’s analysts have blocked approximately 100,000 domains associated with Darcula 2.0 and identified 20,000 phishing websites along with 31,000 IP addresses linked to the platform.
The evolution of services like Darcula highlights the ever-growing need for continuous advancements in cybersecurity measures and increased user awareness. As attackers employ increasingly sophisticated techniques, security professionals and organizations must respond swiftly by adopting cutting-edge protective strategies and reinforcing defensive infrastructures.