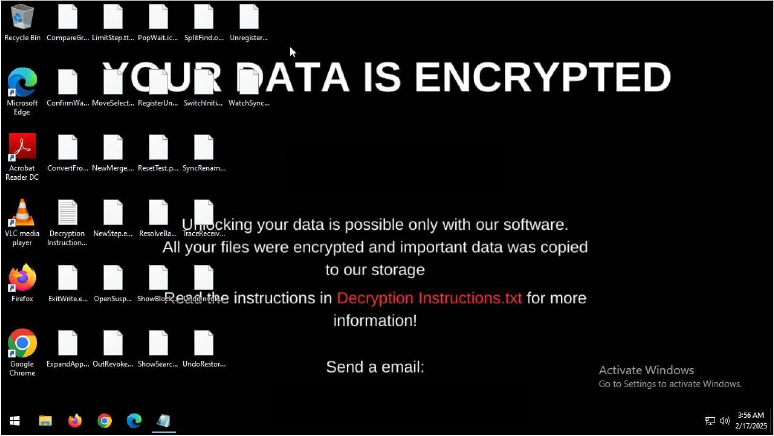
CYFIRMA researchers have uncovered a new cyber threat—the Vgod ransomware, which is actively circulating on underground hacker forums. This malicious payload specifically targets Windows operating systems, employing sophisticated encryption techniques and appending the unique “.Vgod” extension to encrypted files.
Upon infiltrating a system, the ransomware immediately encrypts the victim’s data and leaves behind a ransom note titled “Decryption Instructions.txt” on the desktop, detailing the attackers’ demands. Simultaneously, the desktop wallpaper is altered to draw the victim’s attention. The ransom note not only informs the victim of the file encryption but also warns of sensitive data exfiltration, accompanied by the threat of public disclosure—an indication that double extortion tactics are being deployed.
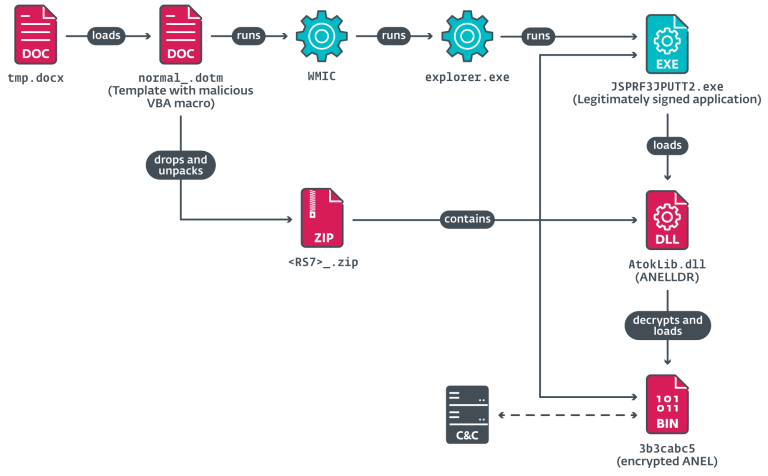
An analysis of Vgod’s behavior reveals its advanced evasion mechanisms. It leverages DLL sideloading to circumvent security protections, injects malicious code into legitimate processes, and manipulates Windows registry settings. The malware also employs stealth techniques, conducting environmental checks to detect virtual machines and sandboxes while executing pre-boot persistence techniques, making it exceptionally resilient to removal.
CYFIRMA experts have mapped Vgod’s tactics to the MITRE ATT&CK framework, identifying the following key techniques:
- Execution methods: PowerShell scripting (T1059.001), Windows API calls (T1106), and DLL execution (T1129).
- Persistence mechanisms: Boot process injection (T1542.003) and DLL hijacking (T1574.002).
- Privilege escalation: Process injection (T1055) and bypassing access controls (T1548).
- Detection evasion: Hidden files, encryption, and system modifications (T1014, T1036, T1112).
- Credential access: Windows password dumping (T1003) and configuration file analysis (T1552.001).
- System reconnaissance: Gathering data on system settings, running processes, and installed applications (T1010, T1082, T1518.001).
- Data exfiltration: Use of encrypted communication channels (T1573) and non-standard protocols (T1095).
- System impact: File encryption (T1486) and misuse of victim’s computing resources (T1496).
Observations suggest that the threat actors communicate with victims via email, likely providing further instructions for ransom payment.
To defend against such ransomware attacks, cybersecurity specialists advise organizations to implement a Zero Trust framework, enforce multi-factor authentication (MFA), and ensure regular system updates. Additionally, maintaining up-to-date backups is critical, allowing for rapid data restoration without engaging in negotiations with cyber extortionists.
Vgod serves as a stark reminder: cybercriminals continuously refine their tools, and security defenses must evolve in tandem. Without a proactive security strategy, every file remains a potential hostage.